G Network Settings for Cybersecurity: A Comprehensive Guide
October is Cybersecurity Awareness Month, a time to raise awareness of the importance of cybersecurity in protecting our networks. In this guide, we'll explore the essential G Network settings for cybersecurity and provide you with a detailed checklist to ensure your network is secure.Why is Network Security Important?
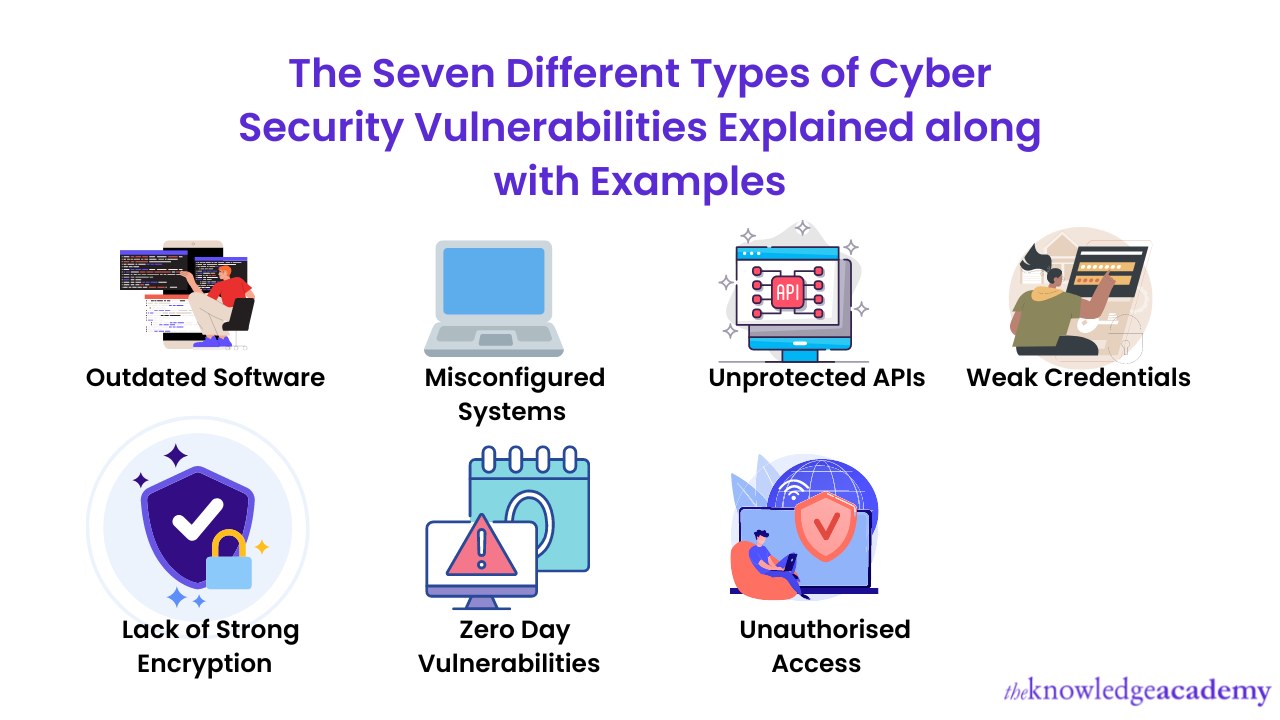
Network security is critical in today's digital age. With the increasing number of cyber threats, it's essential to have a robust security framework in place to protect your network from unauthorized access, data breaches, and malware attacks. A secure network not only protects your sensitive data but also ensures business continuity and reputation.Network Security Checklist
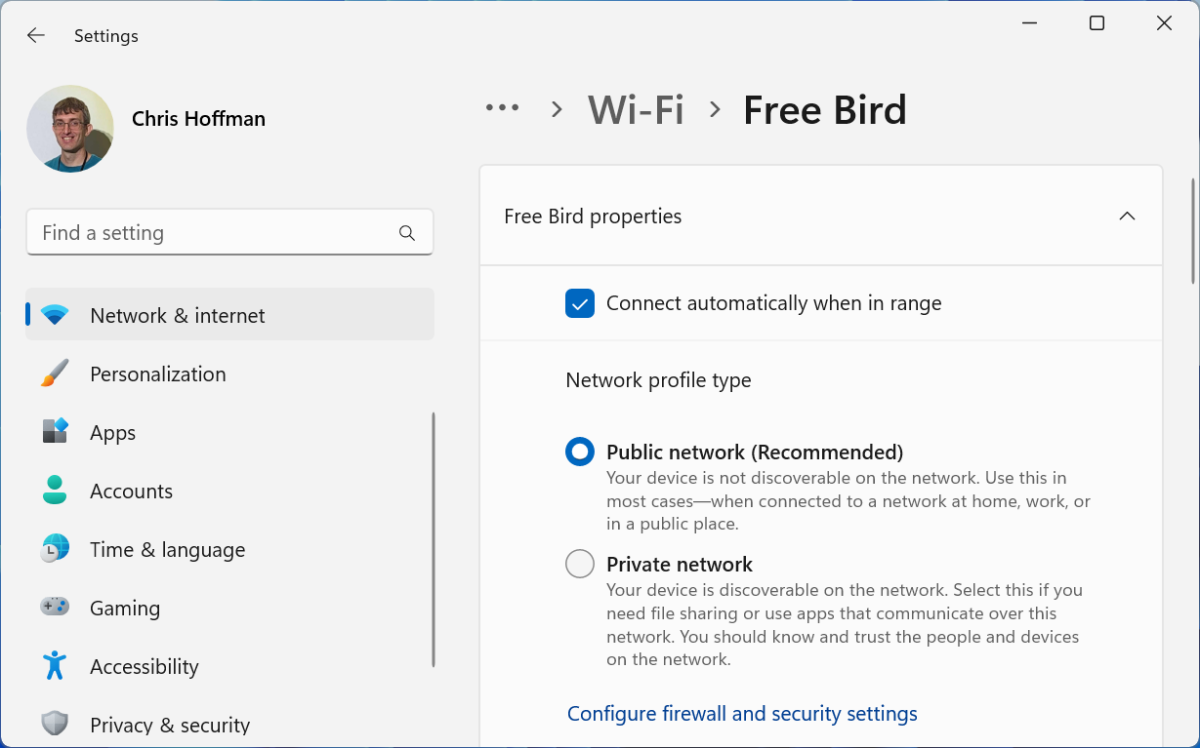
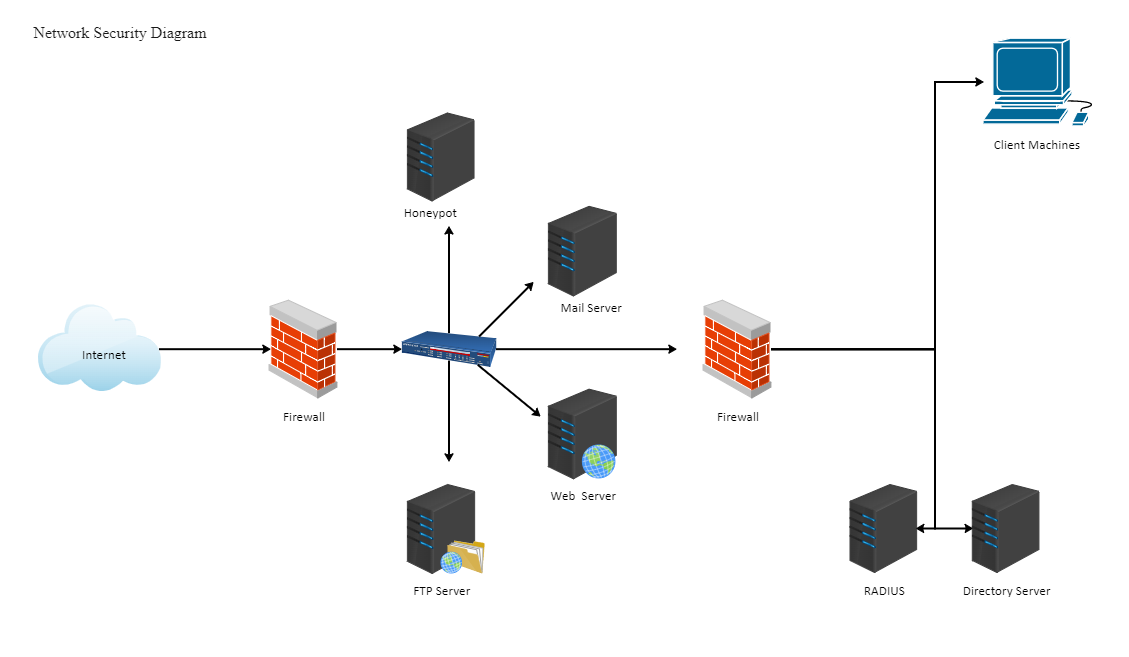
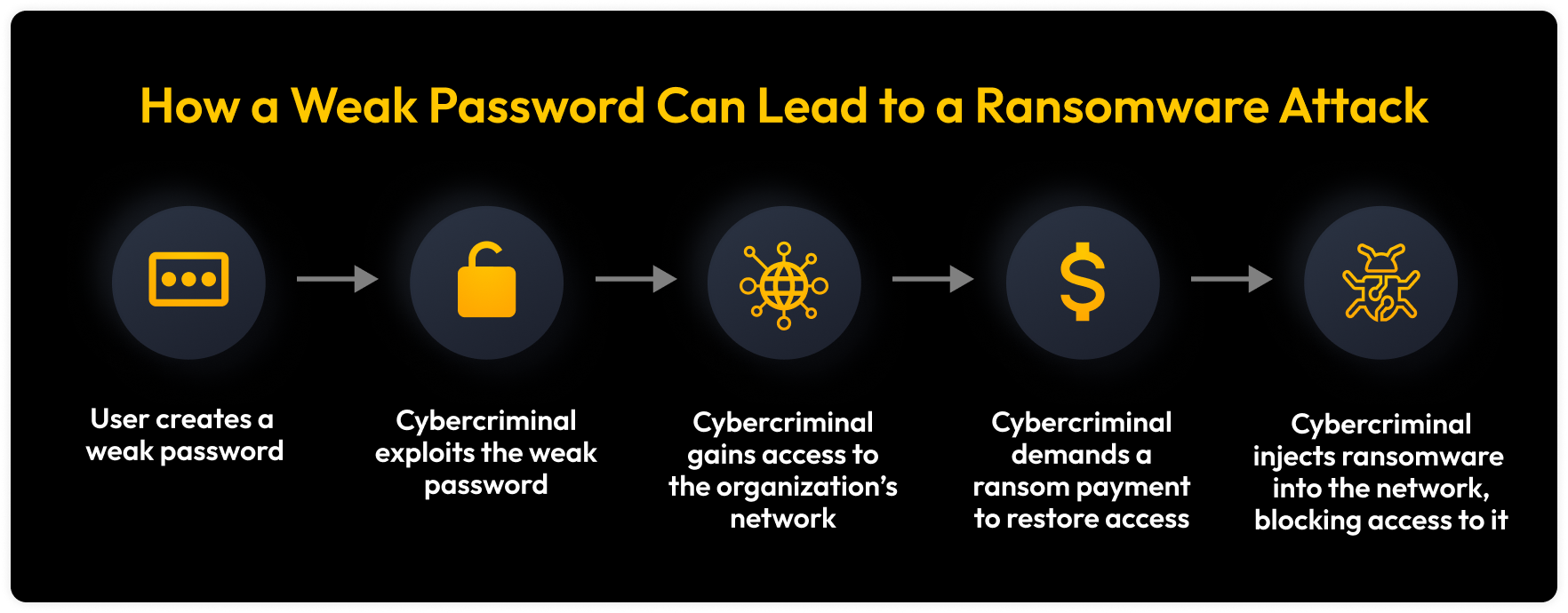
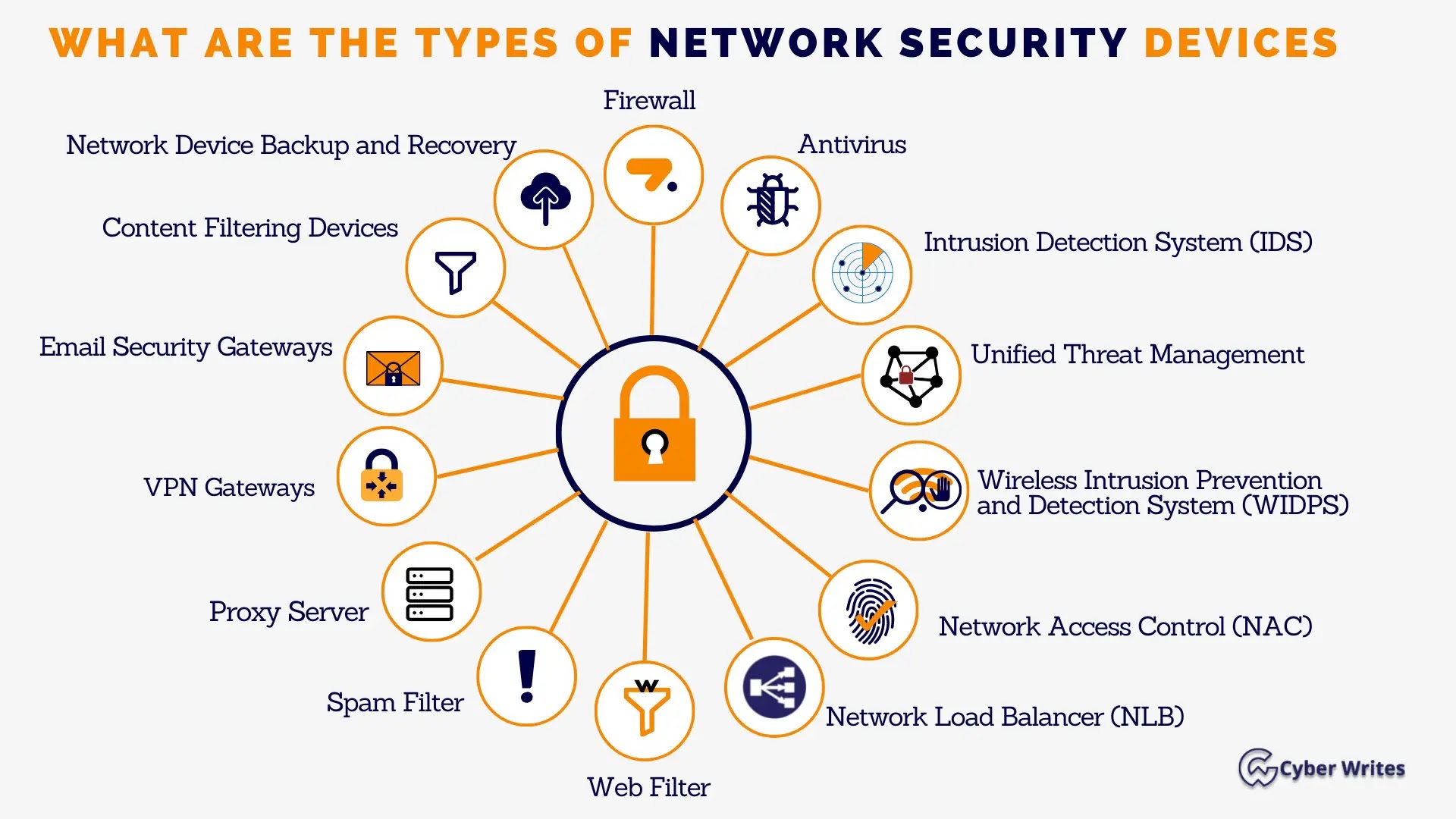
To ensure your network is secure, follow this comprehensive checklist: ### 1. **Change Default Router Login Credentials** Change the default login credentials of your router to prevent unauthorized access. ### 2. **Enable WPA2 Encryption** Enable WPA2 encryption on your router to protect your wireless network from eavesdropping and interception. ### 3. **Set Up Guest Network** Set up a guest network to segregate visitors from your main network and prevent them from accessing sensitive areas. ### 4. **Implement Wireless Network Segmentation** Segment your wireless network to restrict access to specific areas of your network and prevent lateral movement. ### 5. **Enforce Strong Passwords** Enforce strong passwords on all user accounts and devices connected to your network. ### 6. **Configure Firewall Rules** Configure firewall rules to allow only necessary traffic to enter and exit your network. ### 7. **Monitor Network Activity** Monitor network activity regularly to detect and respond to security incidents.Google Network Settings for Cybersecurity