Gallery Photos
How to create a remote network with Global Secure Access
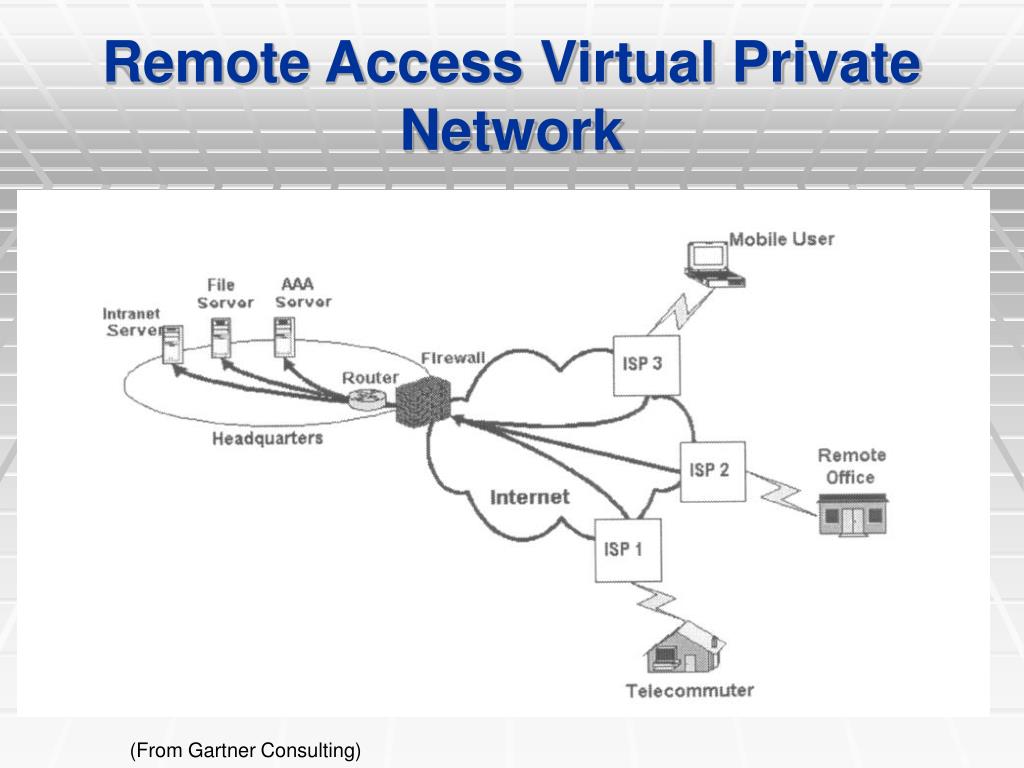
Oct 21, 2025Remotenetworksareremotelocations, such as a branch office, ornetworksthat require internet connectivity. Setting upremotenetworksconnects your users inremotelocations to Global SecureAccess. Once aremotenetworkis configured, you can assign a traffic forwarding profile to manage your corporatenetworktraffic.
entra-docs/docs/global-secure-access/quickstart-remote-network.md at ...
Mar 13, 2026Microsoft Entra InternetAccessisolates the traffic for Microsoft applications and resources, such as Exchange Online and SharePoint Online. Users canaccessthese resources by connecting to the Global SecureAccessclient or through aremotenetwork, such as in a branch office location. This quickstart shows you the steps needed to create aremotenetworkand start acquiring Microsoft ...
Global Secure Access (GSA) Remote Network - AnyViewer
Oct 24, 2025Global SecureAccessremotenetworkhelps organizations connectremoteoffices and workers safely. It uses Microsoft'snetworkto enforce security, reduce delays, and simplifysetup.

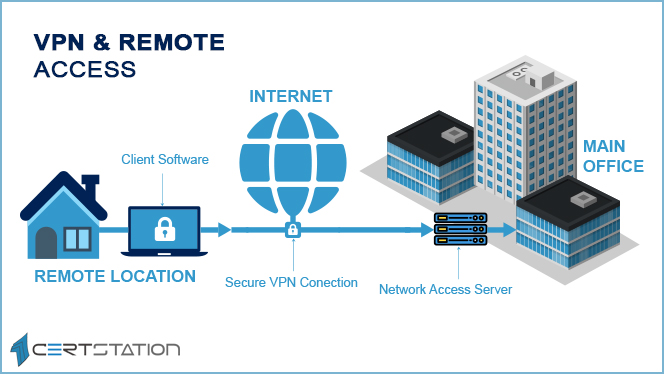
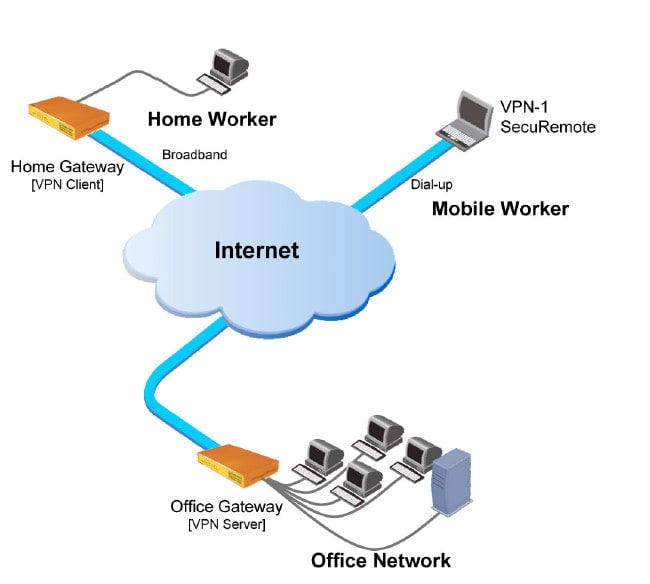
How to set up a secure remote access VPN for home workers
Nov 21, 2024Whether or not you need aremoteaccessVPNsetup to get into the companynetworkand work from home depends on your company'snetworksecurity policy. A new virtualnetworkarchitecture is emerging, called secureaccessservice edge (SASE), which is more appropriate for linking together sites, cloud platforms, andremoteworkers.

How to Set Up a VPN for Remote Access - blog.openvpn.net
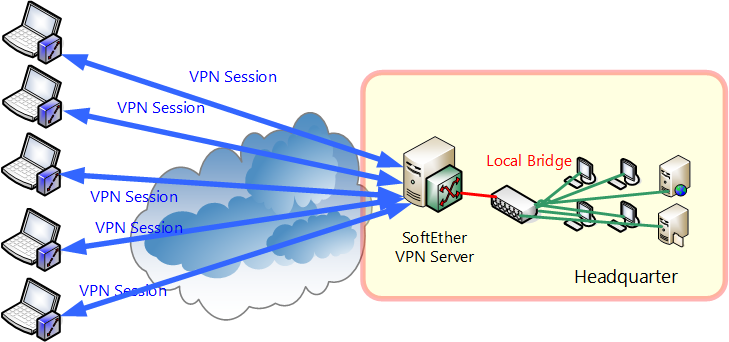
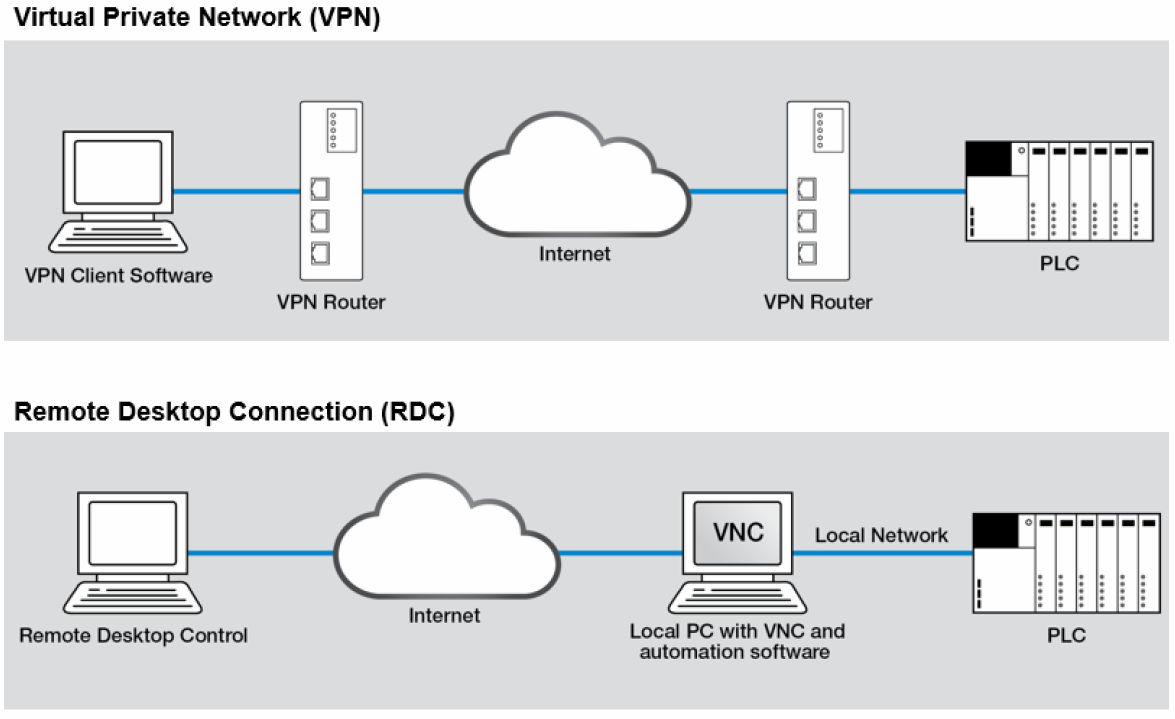
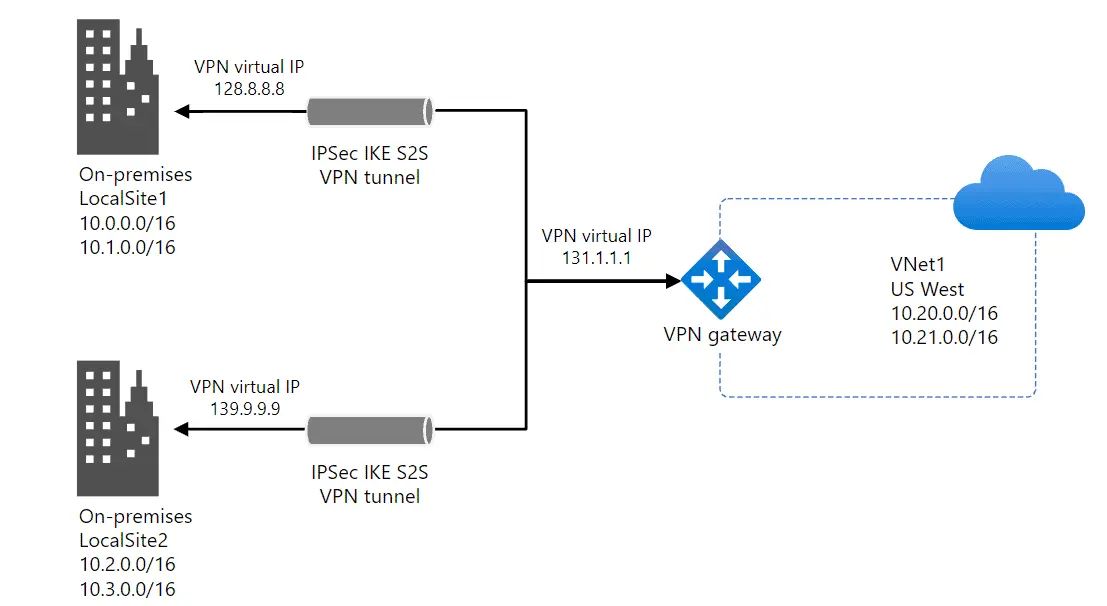
Feb 4, 2026RemoteaccessVPN: Individual users connect to anetwork, typically from personal or company-managed devices outside the office. Site-to-siteVPN: Entirenetworksconnect to each other, creating a permanent link between offices or data centers.
GWN700X - User Manual - Documentation Center
Dec 30, 2025By providing high-performance routing,VPNsupport, powerful security protection, and easy-to-usenetworkmanagement tools, the GWN GigabitVPNrouters are ideal for a wide variety of deployments, including small-to- medium businesses, retail, education, hospitality, healthcare, and more.
Create a Classic VPN connection to a remote site - Google Cloud
5 days agoForexample, you can configure a ClassicVPNconnection to aremotesite such that the on-premises IP address ranges do not conflict with the Google Cloud VM IP address. In this tutorial, you use a Google Cloud project, the Google Cloud console, a virtual machine (VM) instance, ClassicVPN, and a few Linux commands.

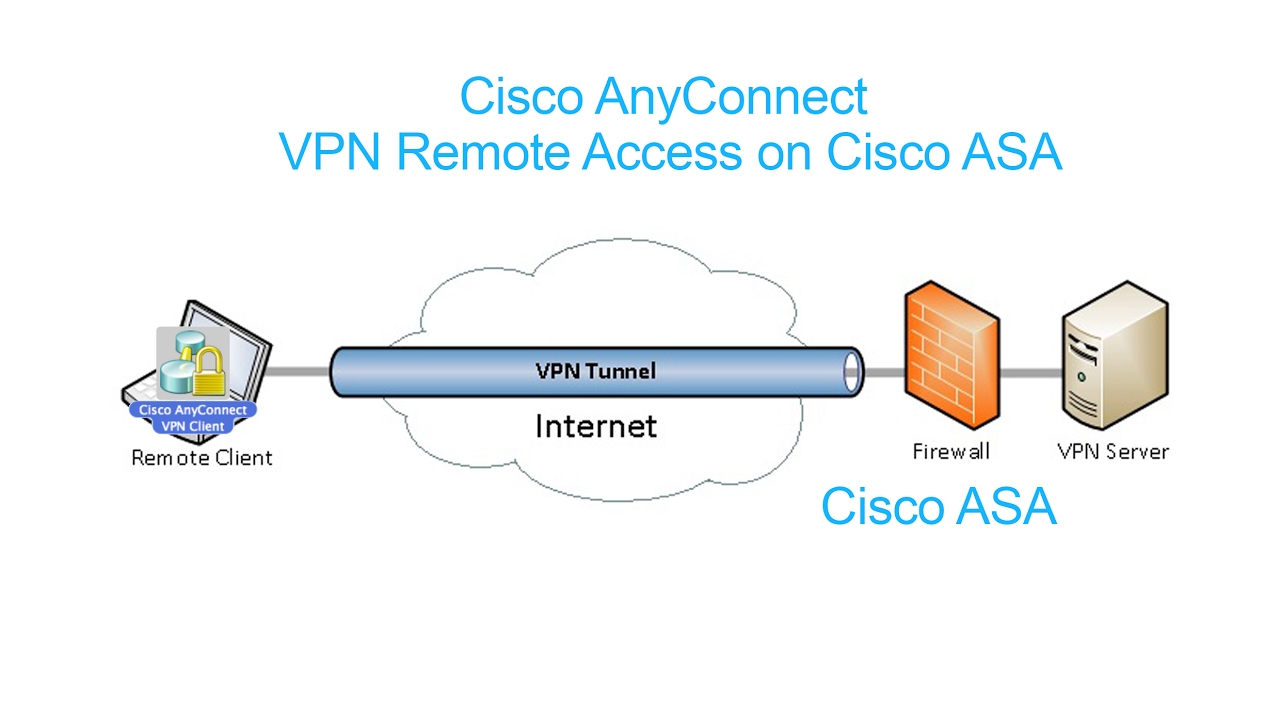
FortiGate IPsec VPN setup for remote users (FortiClient)
Jan 4, 2026This guide walks through building aremote‑accessIPsecVPNon a FortiGate firewall for users connecting with FortiClient. We'll go from user creation, to tunnelsetup, to firewall policies ...

Ghost Network — Programmable Private Networking
Zero-setupencrypted mesh networking for teams, servers, and IoT. Connect everything in seconds with no firewall rules orVPNconfigs.

Remote Access Deployment - Cisco Meraki Documentation
Jul 30, 2025RemoteAccessSetupBefore you begin, first, you'll need to integrate your Cisco Meraki and Cisco Umbrella accounts together for a seamless experience and meet the prerequisites ofremoteaccessdeployment. For further instructions, please check article Cisco Secure Connect Onboarding and Cisco Secure Connect -RemoteAccess.

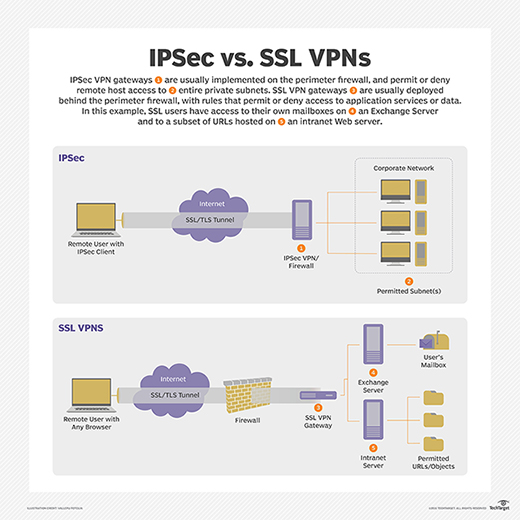
How to Configure SSL VPN: A Comprehensive Guide for Secure Remote Access
TodayIt fundamentally involves setting up a secure tunnel between aremoteuser's device and your privatenetwork, all over the public internet, using SSL/TLS encryption. This guide aims to demystify that process, offering you the insights and steps needed to achieve robust SSLVPNdeployment.

Does VNC Only Work on Local Network? Full Remote Access Guide
5 days agoDiscover if VNC works outside your localnetwork. Learn how tosetup VNC for over-the-internetaccessusing port forwarding,VPNs, and SSH tunneling.
Why a Hardware VPN Is the Better Choice for Remote Access
A hardwareVPNis better than a softwareVPNforremoteaccessbecause it uses your own homenetworkinstead of sharedVPNservers. This provides greater control, a consistent home IP address, and a more stable connection environment over time. HardwareVPNsare designed for users who need reliable, long-termremoteaccesstied to their home internet.
Top 5 Considerations for Working Remote with SOLIDWORKS PDM - LinkedIn
1 day agoInremotescenarios where the internet/VPNwill not be available, Work Offline mod e gives SOLIDWORKS PDM users the ability to "take files home with them" to continue working while away from ...
Virtual private network - Wikipedia
Virtual privatenetworkVPNconnectivity overview, showing intranet site-to-site andremote-work configurations used together A virtual privatenetwork(VPN) is an overlaynetworkthat usesnetworkvirtualization to extend a privatenetworkacross a publicnetwork, such as the Internet, via the use of encryption and tunneling protocols. [1]