G Network Setup for Secure Communication Protocols
In today's interconnected world, ensuring the security of communication protocols is crucial for protecting sensitive data and maintaining the integrity of online transactions. With the rise of cyber threats and vulnerabilities, it's essential to understand the importance of network security protocols like TLS, IPsec, and SSH in safeguarding our online activities. In this article, we'll delve into the world of G Network Setup for Secure Communication Protocols, exploring the nuances of these protocols and how they can be used to protect our online communications.
Basics of Network Security Protocols
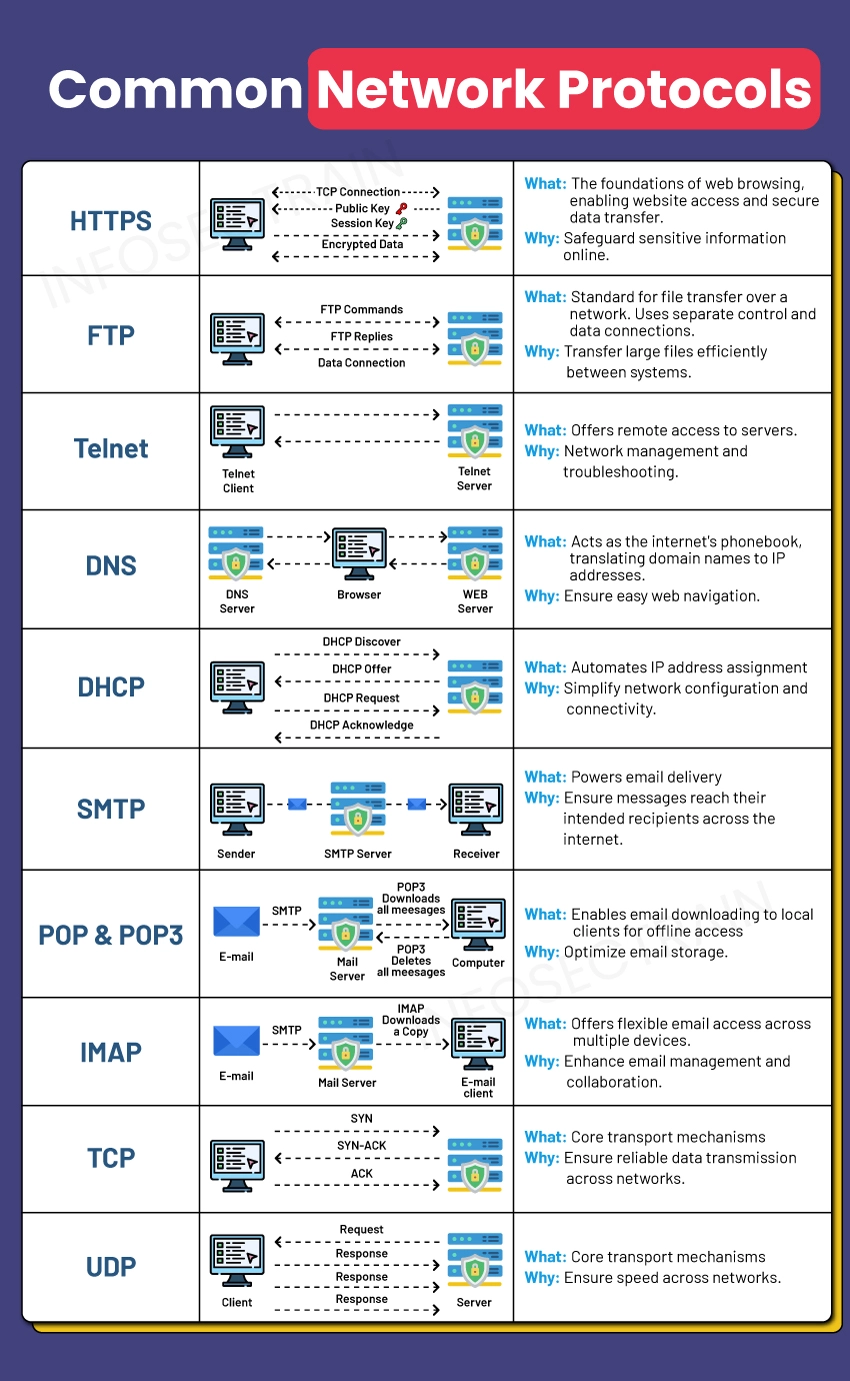
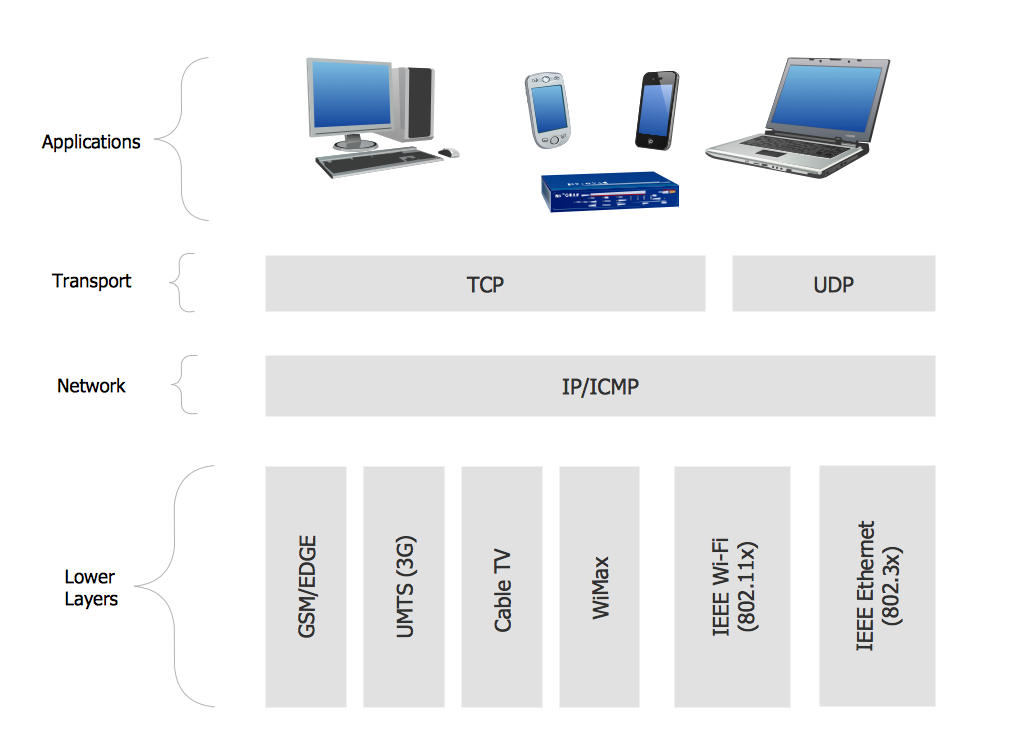
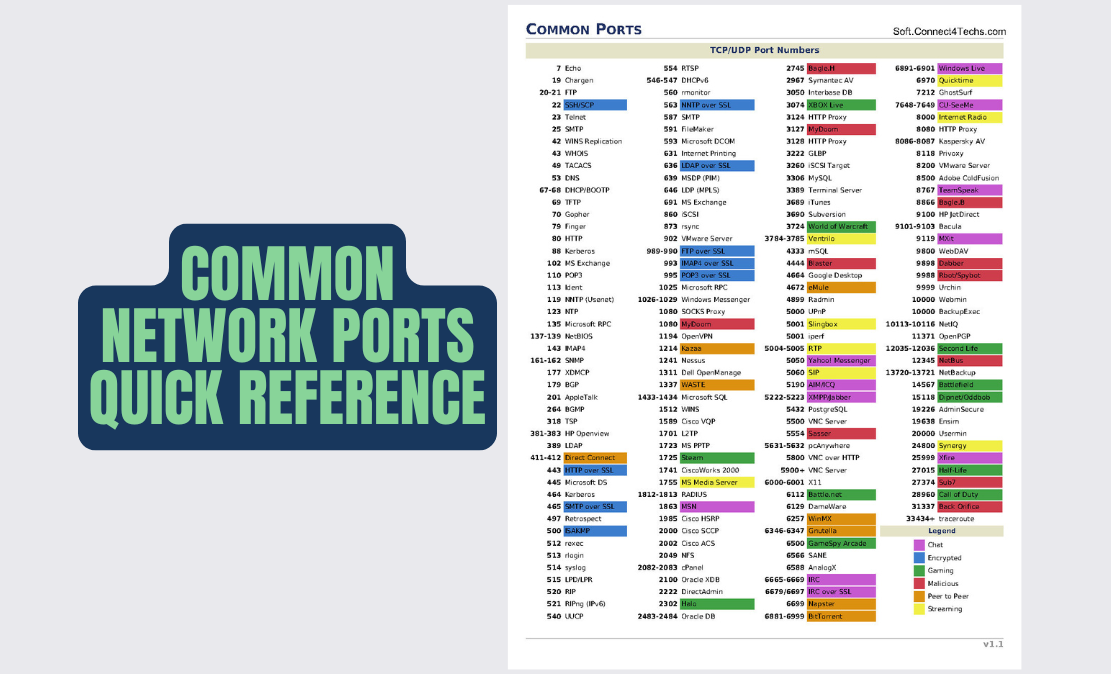
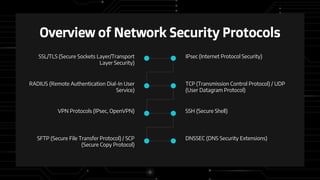
Network security protocols are designed to protect the confidentiality, integrity, and availability of Internet communications between network hosts, gateways, and devices. At the heart of these protocols lie the cryptographic algorithms that ensure the secure transmission of data. Some of the most common network protocols include:
- Internet Protocol Security (IPsec)
- Secure Sockets Layer (SSL)
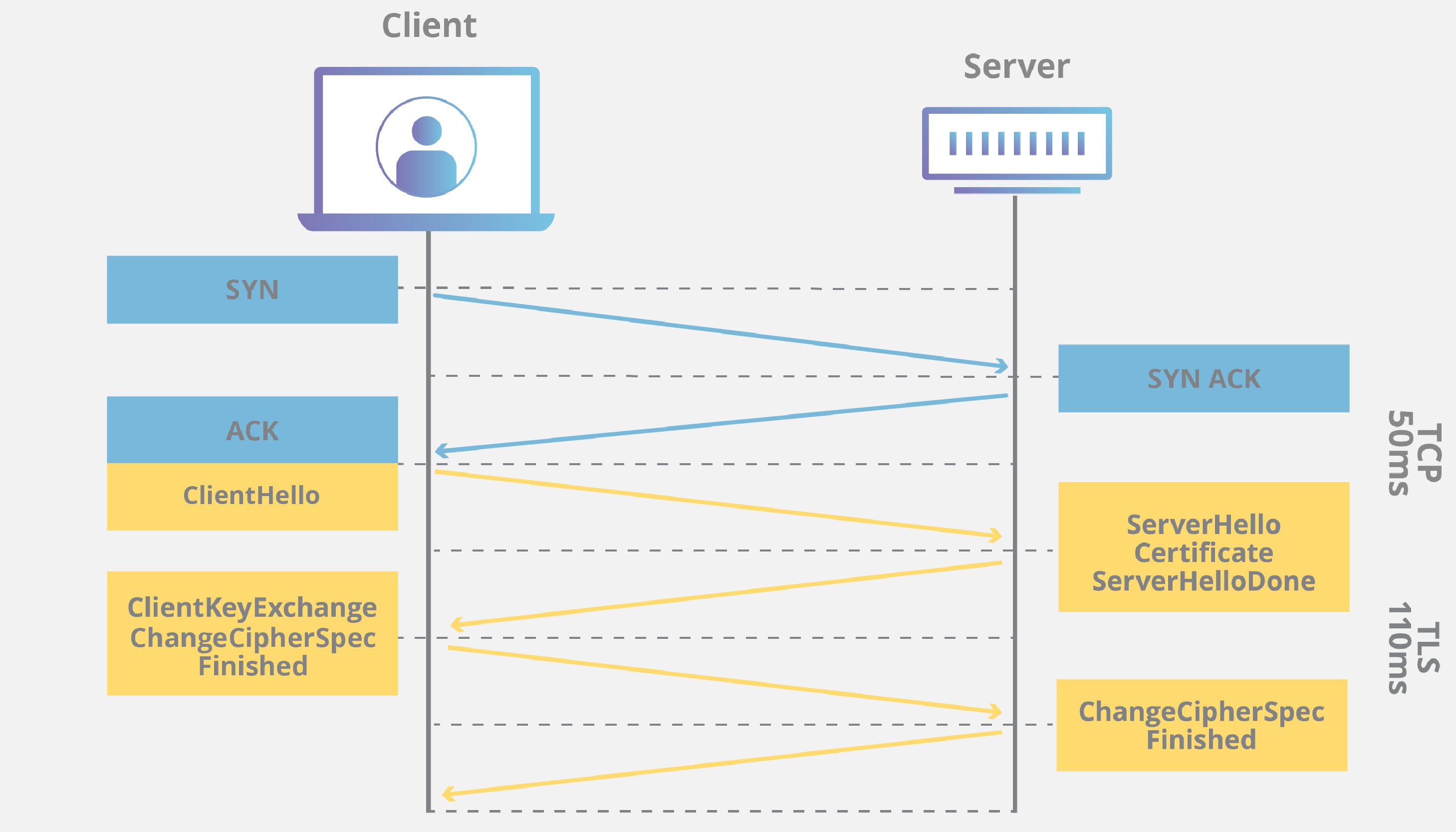
- Transport Layer Security (TLS)
- SSH
- IPSec
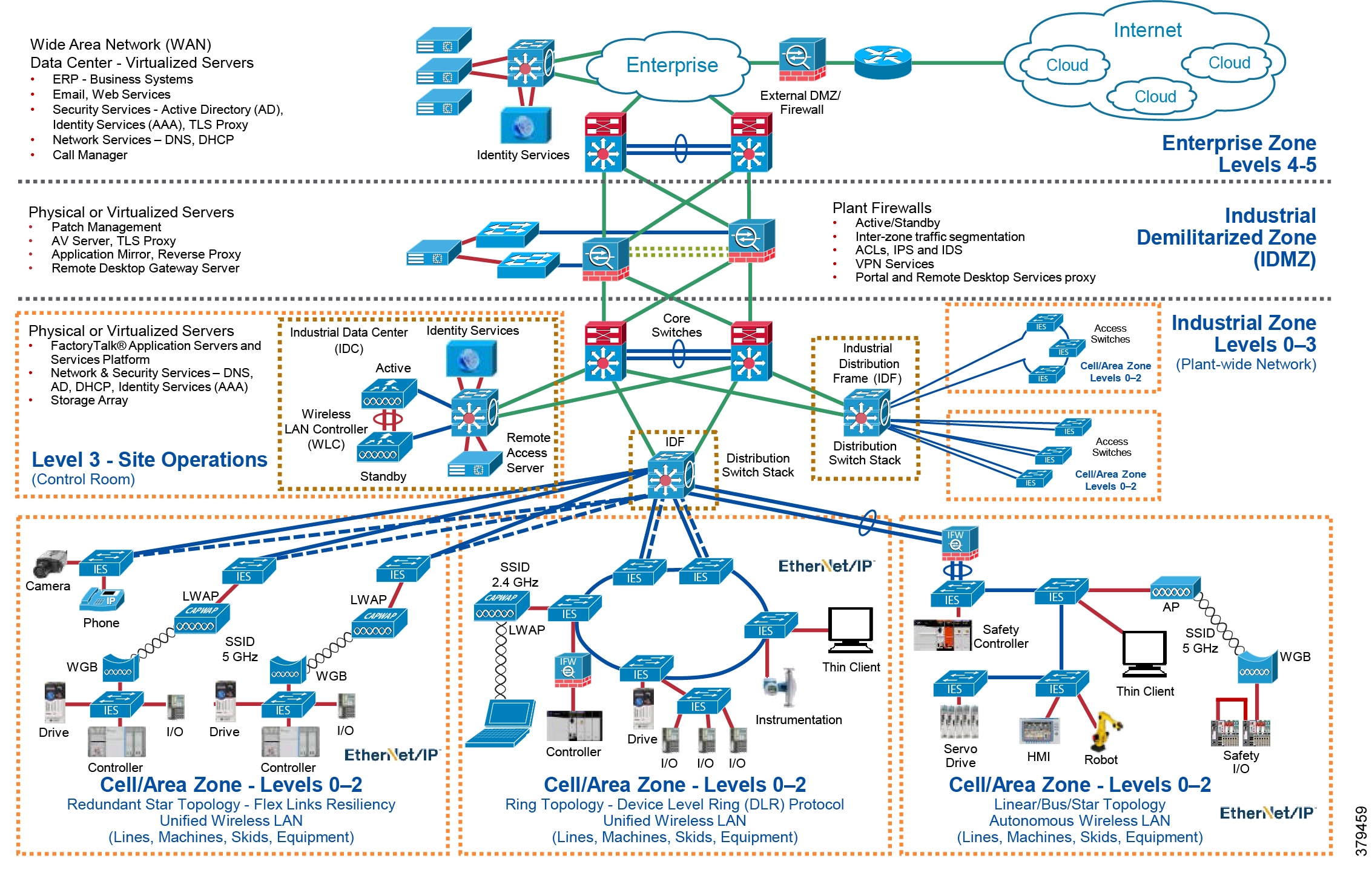
Understanding G Network Setup for Secure Communication Protocols
A G Network Setup for Secure Communication Protocols involves configuring network devices and infrastructure to ensure the secure transmission of data. This includes setting up nodes, routing protocols, and removing vulnerabilities. To achieve a secure network setup, it's essential to:
- Use a combination of encryption algorithms to protect data confidentiality and integrity.
- Implement authentication mechanisms to verify the identity of devices and users.
- Set up secure routing protocols to ensure that data is transmitted securely between network nodes.
Benefits of G Network Setup for Secure Communication Protocols
A correctly set up G Network Setup for Secure Communication Protocols offers numerous benefits, including:
- Improved confidentiality and integrity of data in transit.
- Enhanced security and protection against cyber threats.
- Increased trust and reliability in online transactions.
- Improved compliance with regulatory requirements.
Common Misconceptions about Network Security Protocols
Many organizations believe that simply implementing network security protocols is enough to guarantee security. However, the truth is that bad actors will always seek to exploit vulnerabilities in the network. In fact, 3GPP has specified that all links between 5G core networks must be authenticated. This highlights the importance of understanding the nuances of network security protocols and their limitations.
Real-World Examples of G Network Setup for Secure Communication Protocols
Let's consider two examples of real-world networks that have successfully implemented secure communication protocols:
- Google's use of Transport Layer Security (TLS) to secure communication between Google Nest Wifi or Google Wifi devices and Google.
- The use of IPsec to secure data transferred over public networks like the Internet.
Conclusion
In conclusion, a G Network Setup for Secure Communication Protocols is crucial for protecting sensitive data and maintaining the integrity of online transactions. By understanding the basics of network security protocols, implementing a secure network setup, and understanding the benefits and limitations of these protocols, organizations can safeguard their network from cyber threats and maintain trust and reliability in online transactions. Remember, G Network Setup for Secure Communication Protocols is not a one-time solution, it requires continuous monitoring and updating to ensure the security and integrity of your network.