Secure G Wireless Network Configuration for Utility Companies: A Critical Component of Operational Safety
Robust security is critical for rolling out at scale in today's fast-paced digital world, especially for utility companies that safeguard critical infrastructure. A utility can't operationalize its wireless network at scale if it can't defend itself and its customers against today's cybersecurity challenges. The security architecture needs to be thought all the way through and properly invested in from the outset. Bolting requirements onto a poorly specified security architecture further down the line can lead to significant security risks and operational downtime.
Why Standardized Security Configurations Matter
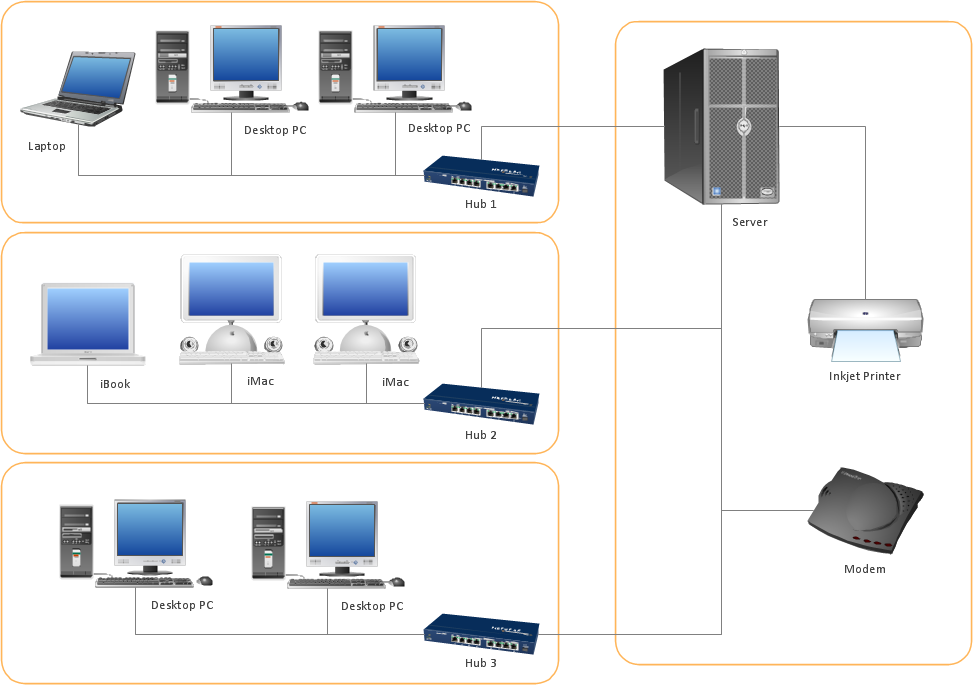
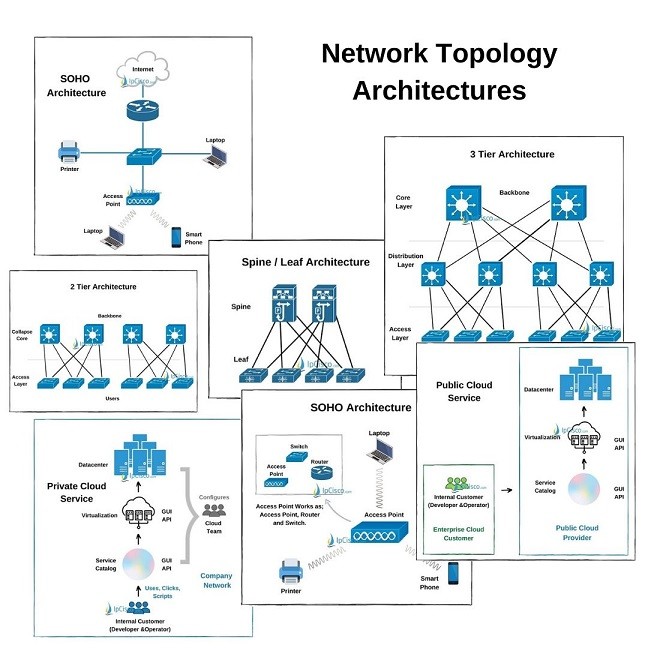
The security of each of the WLAN components, including client devices, APs, and wireless switches, is heavily dependent on their WLAN security configuration. Having standardized security configurations is essential for WLAN components to ensure consistency and uniformity across the network. This section explains why standardized security configurations are important for WLAN components and provides recommendations for designing, implementing, evaluating, and maintaining a secure wireless network.
General Services Administration (GSA) Guidelines
According to the General Services Administration (GSA), the GSA Wireless Local Area Network (LAN) Security policy sets forth the policy on securing wireless Local Area Networks (LANs). This policy is based on industry best practices in securing wireless networks, including 802.11, an evolving family of specifications for wireless LANs (such as in a home or other building) developed by the Institute of Electrical and Electronics Engineers (IEEE).
Securing Utility Company Wireless Networks
Utility companies rely on wireless networks to ensure the reliable delivery of critical services, such as electricity, gas, and water. In this challenging environment, security breach or a cyber attack can have catastrophic consequences. Therefore, securing utility company wireless networks is of paramount importance. Standardized security configurations for WLAN components, such as client devices, APs, and wireless switches, are crucial for maintaining the integrity and security of these networks.
Streamlining Wireless Network Security

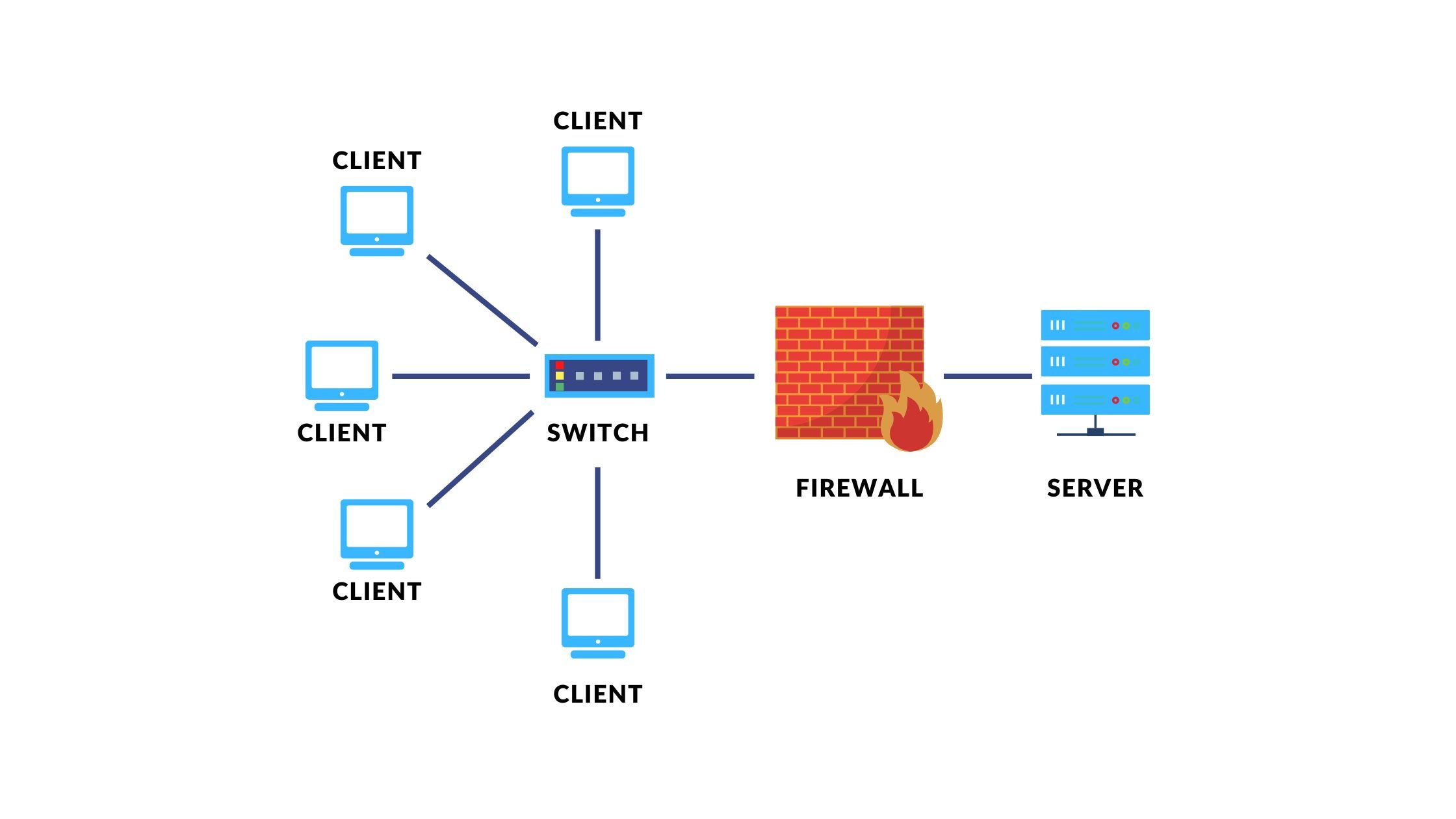
To streamline wireless network security for utility companies, technicians need to design and maintain secure wireless network policies that protect against unauthorized access and vulnerabilities. This includes implementing features such as network segmentation, encryption, access controls, and identity and access management (IAM) solutions. By doing so, utility companies can reduce the risk of security breaches and ensure the uninterrupted delivery of critical services.
Configuring Security Systems
Configuring security systems is a critical component of wireless network security. Utility companies need to invest in robust security systems that can prevent and respond to security threats effectively. This includes implementing intrusion detection and prevention systems (IDPS), security information and event monitoring (SIEM) systems, and endpoint security solutions. By doing so, utility companies can protect their networks and assets from cyber threats and ensure the continuity of operations.
Best Practices for Wireless Network Security
The following best practices for wireless network security should be adopted by utility companies to ensure the secure and reliable delivery of critical services:
-
Implement WPA3, the most secure standard currently available, to ensure data protection and prevent unauthorized access.
-
Use network segmentation to isolate critical systems and protect them from cyber threats.
-
Implement encryption to secure data and protect it from unauthorized access.
-
Use access controls to define who has access to the network and ensure that only authorized personnel can access critical systems.
-
Implement IAM solutions to manage and control user identities and access to network resources.
Conclusion
Securing utility company wireless networks is a critical component of operational safety in today's interconnected world. Standardized security configurations, best practices in wireless network security, and robust security systems are essential for maintaining the integrity and security of these networks. By implementing these measures, utility companies can reduce the risk of security breaches and ensure the uninterrupted delivery of critical services.