Ensuring G Wireless Network Security Configuration for Government
The Importance of G Wireless Network Security Configuration for Government
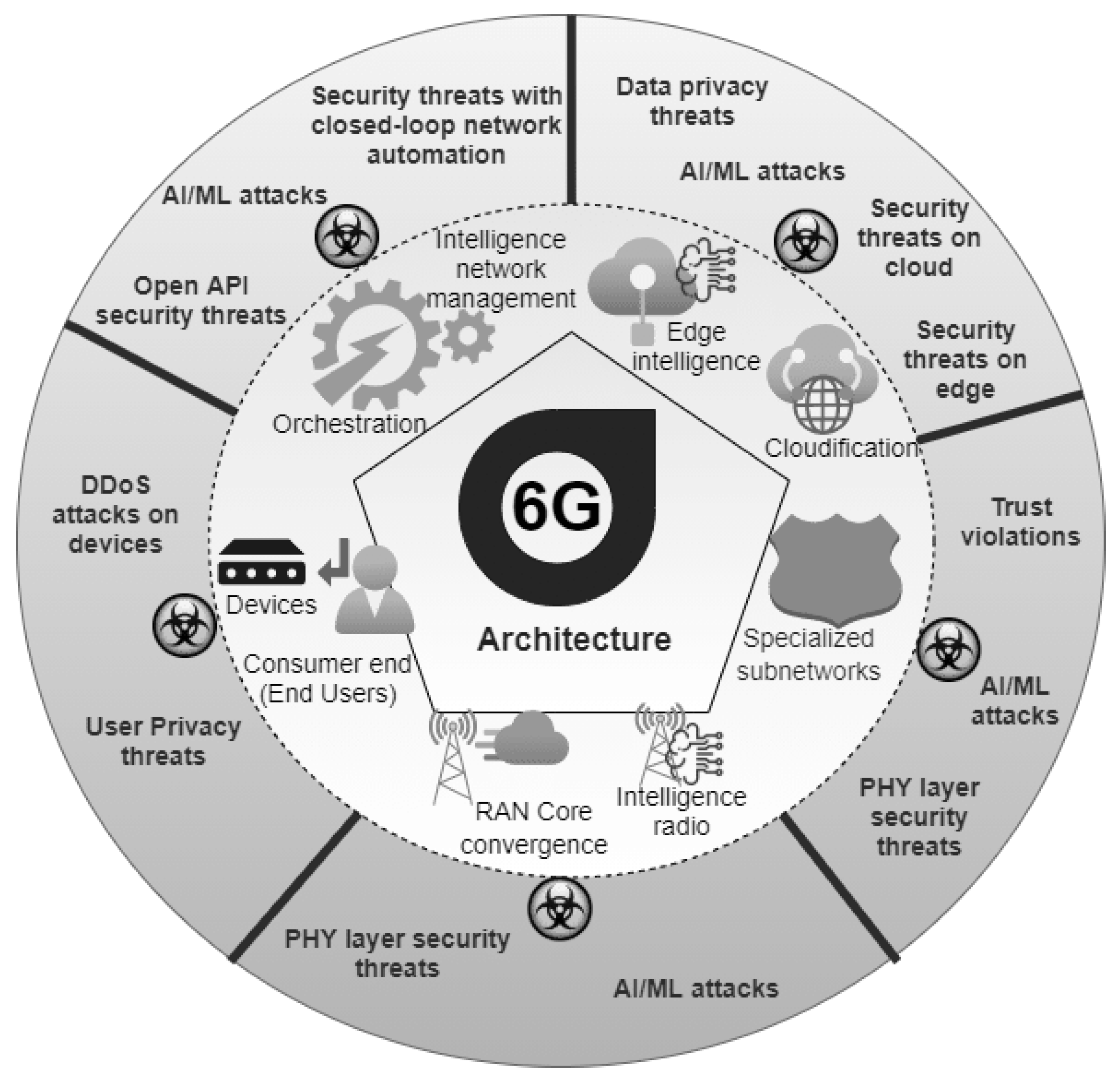
In today's digital age, the use of wireless networking technologies has become an essential part of government operations. With the growth of mobile devices and the increasing need for mobility, wireless networks have become a crucial component of modern government infrastructure. However, with the benefits of wireless networks come inherent security risks that need to be addressed. A well-configured wireless network is not only essential for the security of sensitive government information but also for the overall functioning of the network.Understanding Wireless Technology
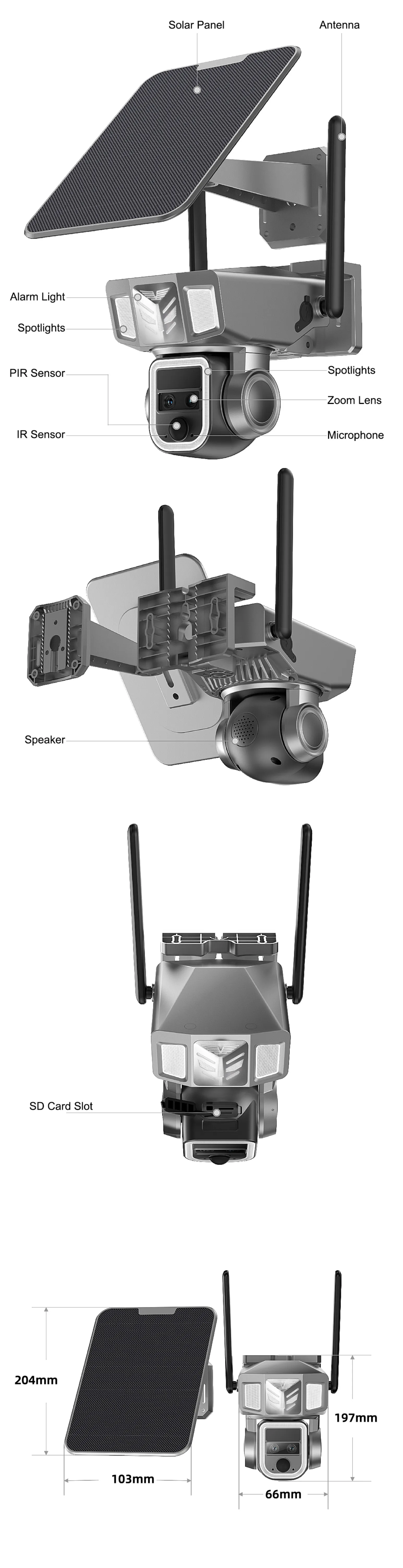
Wireless technology is a broad term that encompasses various forms of wireless communication, including Bluetooth, infrared, and wireless computer peripherals. Smart devices such as smart refrigerators, medical pumps, and wireless-enabled hearing aids also fall under this category. To protect information systems and data on those systems, it is essential to have a standardized security configuration for WLAN components, including client devices, APs, and wireless switches.GSA Wireless Local Area Network (LAN) Security
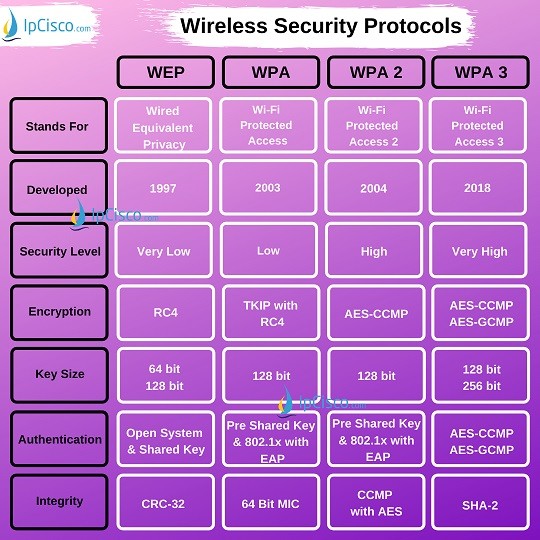
The General Services Administration (GSA) has set forth a policy on securing wireless local area networks (LANs) based on industry best practices in securing wireless networks, including 802.11. This directive provides guidelines for securing wireless networks and ensures that sensitive information is protected. Key aspects of GSA wireless LAN security include:- Using encryption protocols such as WPA2 or later
- Implementing strong passwords and password policies
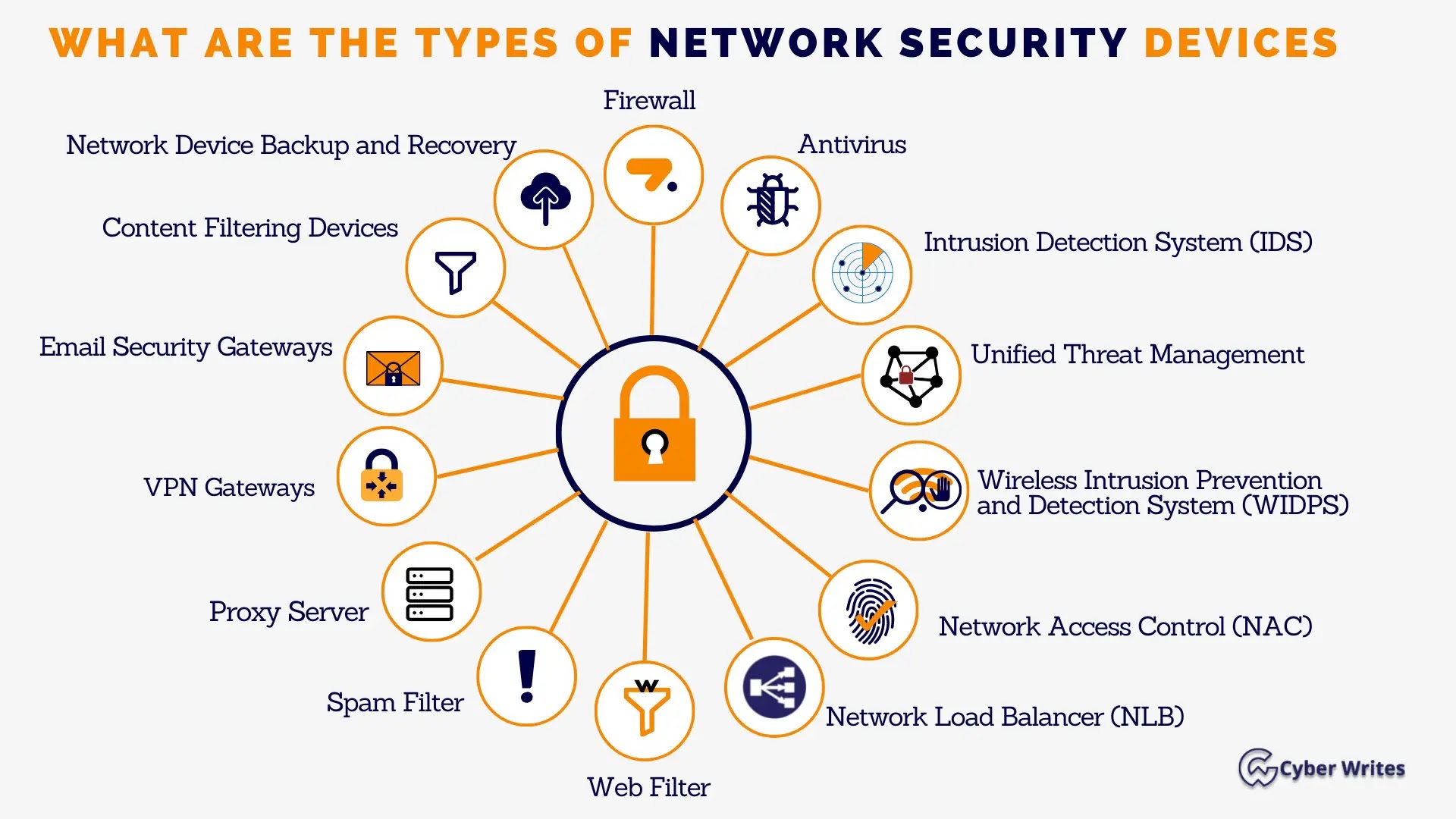
- Configuring wireless networks to require network access control (NAC)
- Regularly monitoring and updating network security controls
- Conducting regular network penetration testing and vulnerability assessments

Wireless Network Security Best Practices
To ensure the security of a wireless network, various measures can be taken. Some of the key best practices include:- Implementing a centralized wireless management structure integrated with the management of the existing wired network
- Ensuring encryption and secure authentication
- Restricting access to authorized personnel and devices
- Using a wireless network segmentation strategy to isolate sensitive data
- Conducting regular security assessments and risk analysis