Wireless G Network Setup for Cybersecurity Training: A Comprehensive Guide
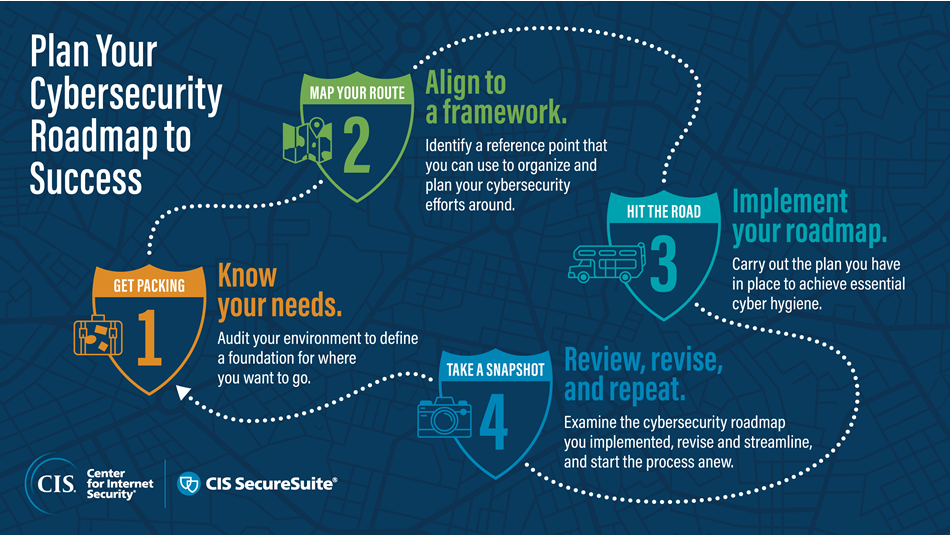
The increasing threat of cyber attacks has made it essential for individuals and organizations to prioritize cybersecurity training. A crucial aspect of cybersecurity training is setting up a secure network environment, and in this article, we will focus on Wireless G Network Setup for Cybersecurity Training.
Why Wireless G Network Setup is Crucial for Cybersecurity Training
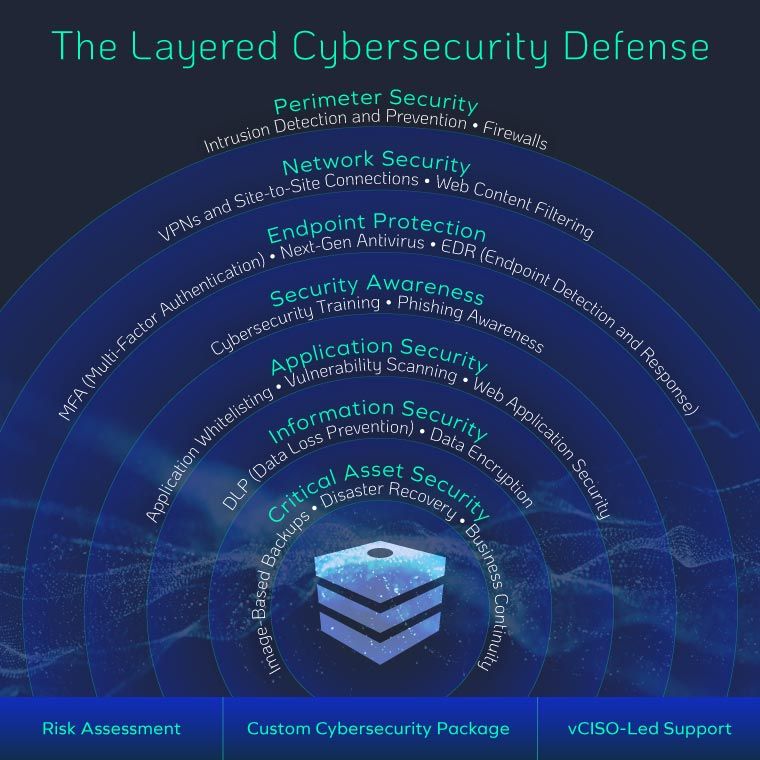
Cybersecurity training requires a robust network setup to ensure that the training environment is secure and reliable. Wireless G network setup is a critical aspect of this process, as it provides a stable and high-speed connection for training purposes. A well-configured Wireless G network setup can help prevent cyber threats and ensure that the training environment is secure.
The Problem with Unsecured Wireless Networks
Unsecured wireless networks are vulnerable to cyber threats, including hacking, data breaches, and malware attacks. Cyber threat actors can exploit unsecured wireless networks to gain unauthorized access to sensitive information, disrupt business operations, and compromise data integrity. Therefore, it is essential to secure wireless networks to prevent these types of threats.
Setting Up a Secure Wireless G Network for Cybersecurity Training
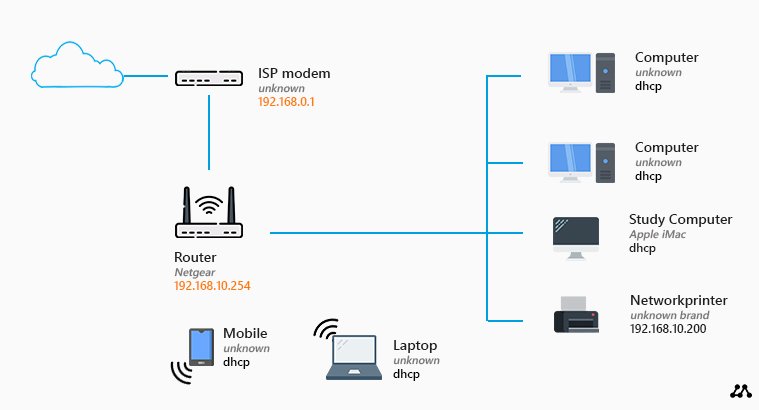
To set up a secure wireless G network for cybersecurity training, follow these steps:

- Choose a Secure Router:** Select a router that supports WPA2 encryption and has a strong password policy.
- Configure WPA2 Encryption:** Configure WPA2 encryption on your router to ensure that all wireless devices connected to the network are encrypted.
- Set up a Strong Password Policy:** Set up a strong password policy on your router to ensure that all users have unique and complex passwords.
- Implement Access Control:** Implement access control measures to ensure that only authorized users can connect to the network.
- Regularly Update Firmware:** Regularly update your router's firmware to ensure that you have the latest security patches and features.
Best Practices for Wireless G Network Setup
Here are some best practices to follow when setting up a Wireless G network for cybersecurity training:
- Use a Guest Network:** Use a guest network to isolate guest devices from the main network and prevent them from accessing sensitive information.
- Use a VPN:** Use a Virtual Private Network (VPN) to encrypt data transmitted over the wireless network.
- Implement Network Segmentation:** Implement network segmentation to isolate sensitive information and prevent it from being accessed by unauthorized users.
- Regularly Monitor Network Activity:** Regularly monitor network activity to detect and respond to potential security threats.
Conclusion
In conclusion, Wireless G network setup is a critical aspect of cybersecurity training. A secure wireless G network setup can help prevent cyber threats, ensure data integrity, and provide a reliable training environment. By following the steps and best practices outlined in this article, you can set up a secure wireless G network for cybersecurity training and ensure that your training environment is secure and reliable.





![Best Network Security Courses & Certificates [2026] | Coursera Best Network Security Courses & Certificates [2026] | Coursera](https://noursolution.com/wp-content/uploads/2025/06/Business-Setup-in-Saudi-Arabia-5.jpg.webp)