Ensuring G Wireless Network Secure Data Sharing: A Comprehensive Guide
As wireless technologies continue to advance, securing data sharing over G wireless networks has become increasingly important. With the rise of IoT devices, cloud computing, and mobile applications, the need for robust security measures has never been more pressing. In this article, we will explore the best practices for securing G wireless network data sharing and provide a comprehensive guide to help you protect your network and data.
The Risks of Unsecured Wireless Networks
Wireless networks introduce additional security risks, making it easier for hackers to intercept data and gain unauthorized access to your network. The risks include:
- Malware and virus attacks
- Unsecured Wi-Fi connections
- Man-in-the-middle attacks
- Insider threats
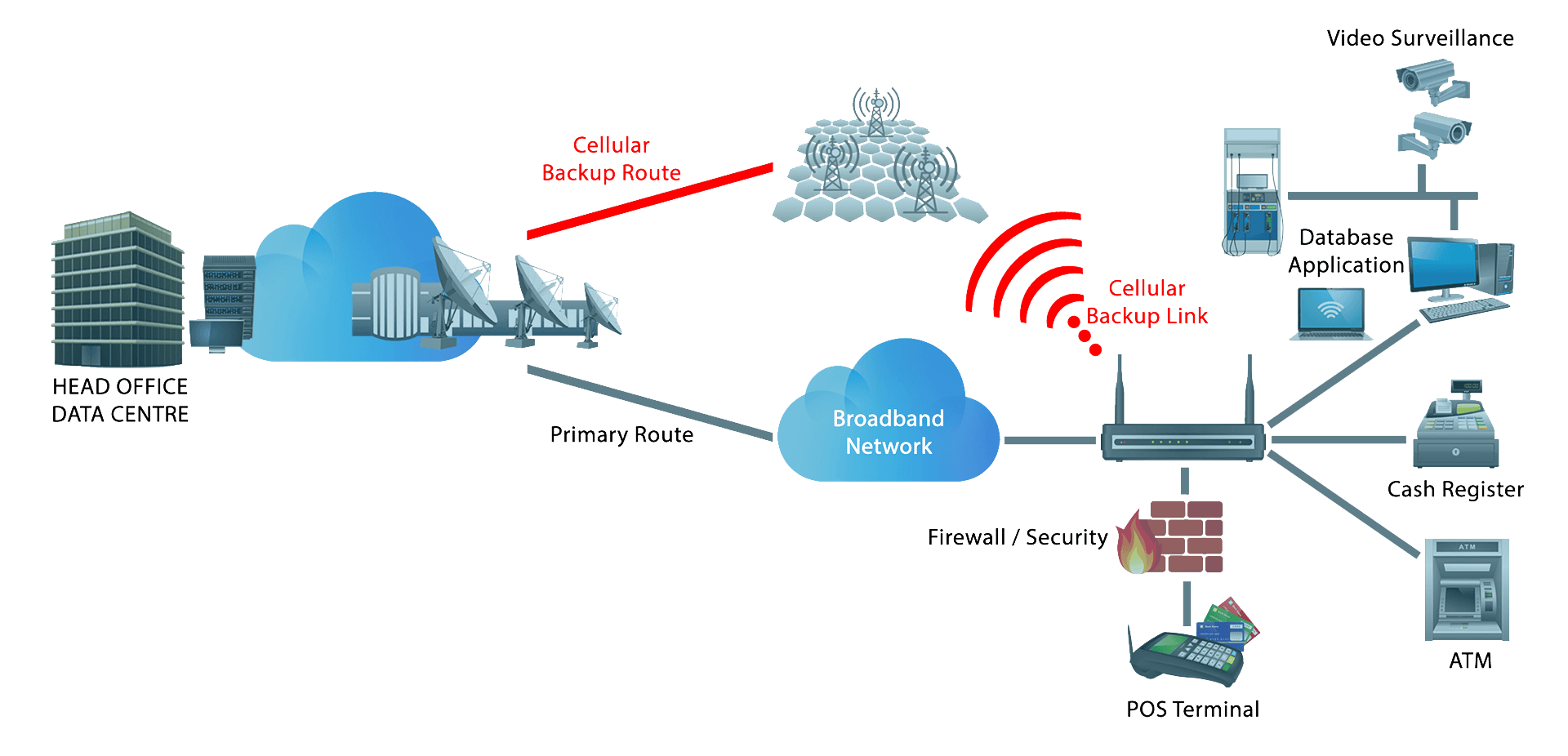
Wireless Security Protocols
Wireless security protocols have evolved over time to address issues, enhance compatibility, and strengthen security. Some of the most common security protocols used in wireless networks include:
- WEP (Wired Equivalent Protocol)
- WPA (Wi-Fi Protected Access)
- WPA2 (Wi-Fi Protected Access 2)
- WPA3 (Wi-Fi Protected Access 3)
Advanced Encryption Algorithms
Advanced encryption algorithms are used to protect data transmitted over wireless networks. Some of the most commonly used encryption algorithms include:
- AES (Advanced Encryption Standard)
- WPA2
- WPA3
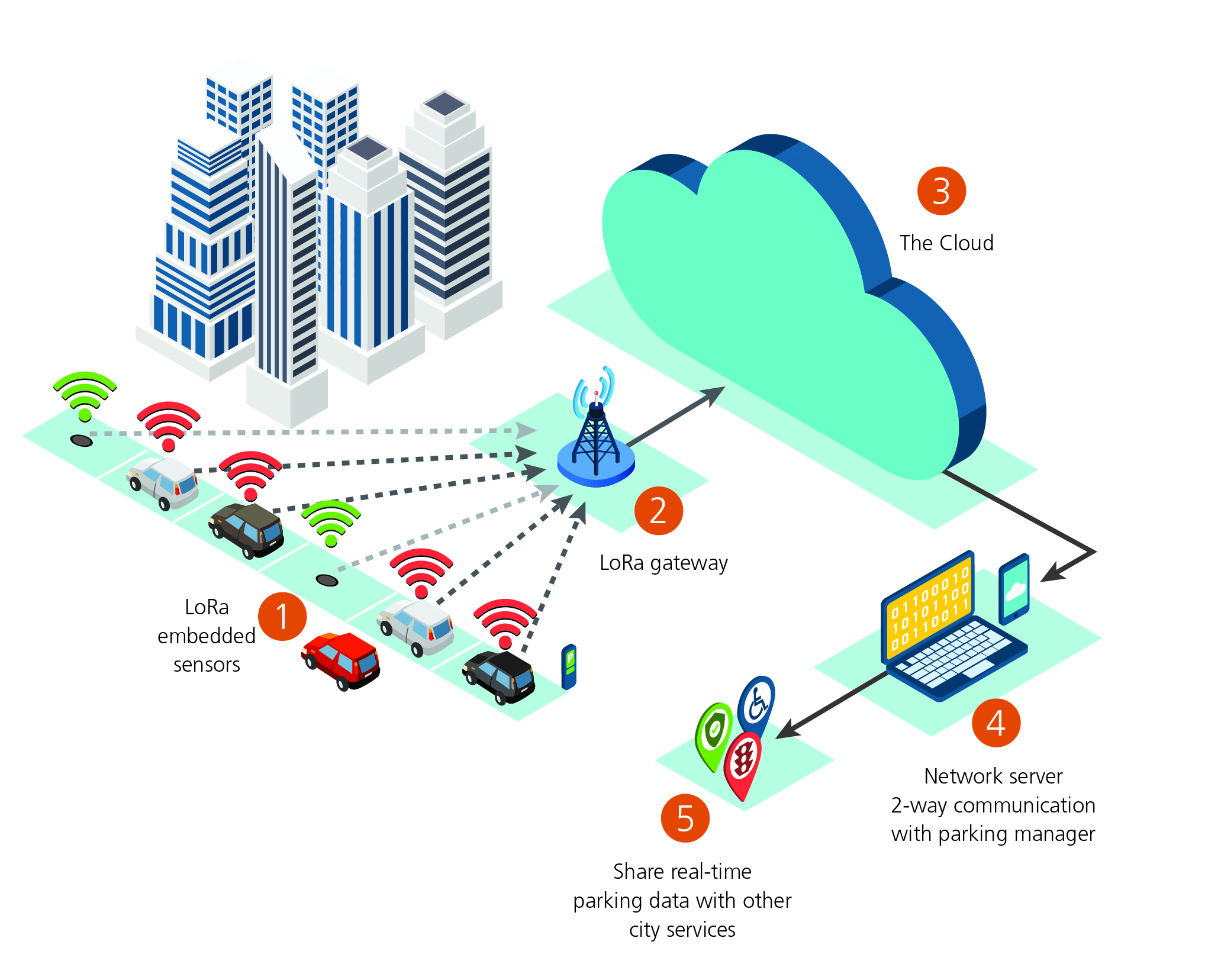
Cloud Security Best Practices

Cloud security best practices are essential for securing data sharing over G wireless networks. Some of the best practices include:
- Implementing robust access controls
- Using encryption for data at rest and in transit
- Regularly updating and patching software
- Monitoring and logging network activity
Wireless Network Security Tips
To secure your G wireless network, follow these best practices:
- Use WPA3 encryption
- Set up a guest network
- Change the default admin password
- Limit network access
- Regularly update and patch software
Conclusion
Securing data sharing over G wireless networks is critical for protecting sensitive information and preventing unauthorized access to your network. By following the best practices outlined in this article, you can ensure the security and integrity of your data and protect your wireless network from potential threats.
Additional Resources
For more information on securing your G wireless network, check out these additional resources:
- Wireless security whitepapers
- Cloud security best practices
- Wireless network security tips